May 4, 2026 | Draxis.ai, the AI-first cyber risk intelligence platform, today announced the general availability of the AI Drop Zone and the paired AI Drop Zone S3 puller. Together they close the gap that every security program eventually runs into: the long tail of tools, reports, and exports that don't justify a structured connector but still carry real risk signal.
Without the Drop Zone, that signal dies in someone's inbox. With it, any artifact you can paste, upload, push, or drop into a bucket becomes typed KRI values in your Risk Register, with citations, and flows through the same risk model the connector data does.
The Long-Tail Problem
Every security program has a stack of tools that matter but never get wired into anything. The regional SIEM that doesn't have an API. The vendor SOC 2 that arrives as a 47-page PDF. The pentest report from last quarter. The auditor's exception list. The configuration export from a niche scanner. The screenshot a partner sent over Slack.
The signal in those artifacts is real. The cost of building a structured connector for each one is not.
Until now, the typical answer was an analyst with a spreadsheet and good intentions, which means most of the signal never made it into the Risk Register at all. The AI Drop Zone replaces that workflow with a single ingestion surface that knows the canonical catalog and extracts against it.
How the AI Drop Zone Works
The Drop Zone accepts artifacts through three intake paths, persists each one keyed by SHA-256, and runs a single bounded LLM pass against the Draxis canonical signal allow-list. Confidence and evidence are both required for auto-accept. Every accepted value cites the literal source span it was derived from.
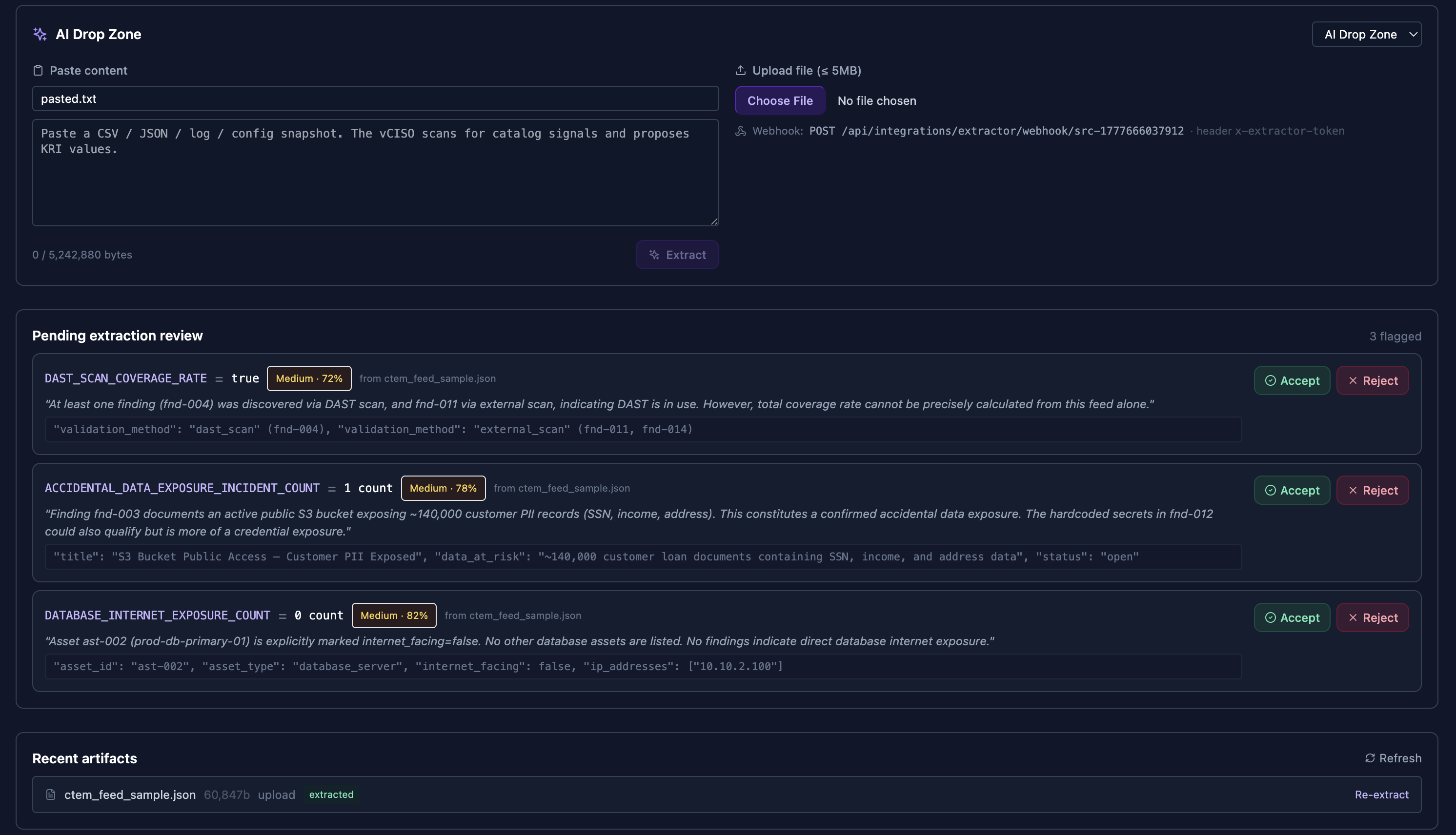
1. Paste, Upload, or Webhook
Open Settings → Integrations → AI Drop Zone, paste a CSV, JSON, log, or config snapshot directly into the textarea, or drag a file (up to 5 MB of plain text, CSV, JSON, YAML, NDJSON, log, or TSV) into the upload zone. For programmatic pushes, every Drop Zone integration gets a webhook URL and a bearer token issued at save. The endpoint is idempotent on SHA-256, so pushing the same payload twice is a no-op, never a duplicate extraction.
2. AI Extraction Against the Catalog
Claude Sonnet scans the artifact body against the Draxis canonical signal allow-list (P1 and P2 catalog signals, bounded at 80 entries per scan) and proposes structured {signal_name, value, unit, confidence, reasoning, evidence} for each match. The evidence field is the literal source span (up to 200 characters) the value was derived from, so an auditor can trace any KRI back to the line of the document it came from.
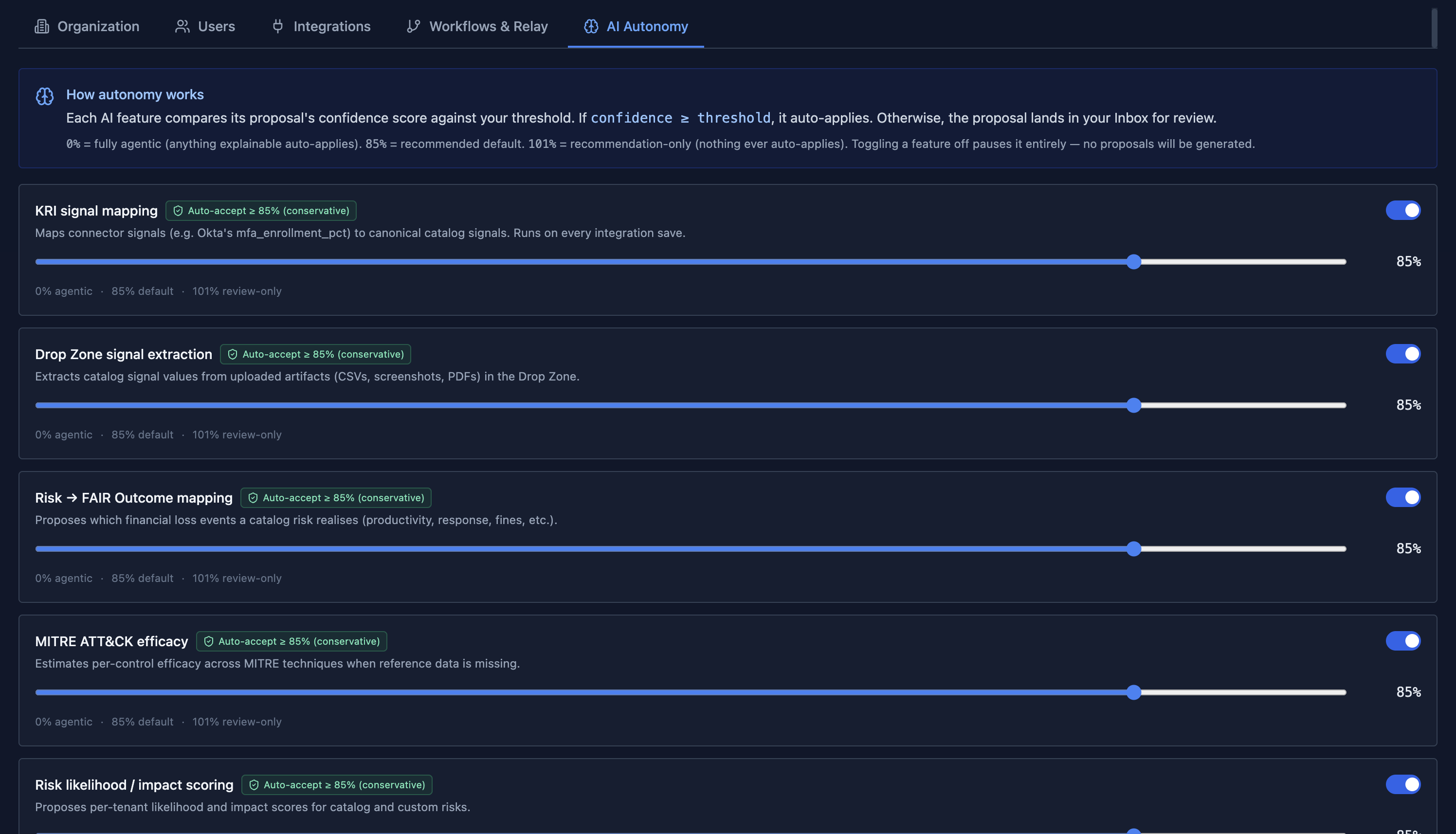
3. Confidence-Gated Auto-Accept
Proposals with confidence at or above 0.85, with non-empty reasoning and a non-empty evidence span, auto-accept and materialize as KRI rows on the integration's next run. Anything below queues in Pending extraction review for inline accept or reject. A high-confidence proposal with empty evidence is treated as low-confidence and queued, the bar is high on purpose.
What the Drop Zone Can Land
The Drop Zone is not bound to a fixed KRI list. It can write to any P1 or P2 signal in the Draxis canonical risk catalog, which today covers 180 KRI signals across 42 risks and 10 domains. What lands in your Risk Register is determined by what the AI finds in the artifact, not by a hardcoded mapping.
A few of the patterns we see during pilots:
- A pentest report listing "3 critical findings, oldest 47 days" lands values for
pentest_critical_findings_openandpentest_critical_age_days_max - A vendor SOC 2 attesting to MFA enforcement on privileged accounts lands a value for
vendor_mfa_privileged_attested - A KnowBe4 PDF export with a phishing-prone percentage lands a value for
kb4_phishing_prone_pct, the same signal the structured KnowBe4 connector populates - A regional SIEM's CSV export of unacknowledged notable events lands a value for
siem_notable_unack_4h
If the AI proposes a signal that isn't in the catalog yet, the proposal routes to the platform-scope Catalog Proposals queue, a candidate addition for the next catalog release. The catalog itself becomes a feedback loop: real artifacts from real customers shape what the platform learns to extract next.
The S3 Puller: Scheduled, Multi-Folder Ingestion
Alongside the manual Drop Zone, Draxis is shipping the AI Drop Zone S3 puller, a connector that watches one or more S3-compatible buckets on your chosen cadence and feeds files into the same extractor. It works against AWS S3, Cloudflare R2, MinIO, and Wasabi out of the box.
Each integration row points at one bucket and one prefix. Each prefix becomes its own virtual integration, with its own calibration profile and run history, so a folder of pentest reports and a folder of vendor SOC 2s stay cleanly separated even if both feed the Drop Zone extractor underneath.
First-Run Calibration
S3-pulled artifacts come from your tools, in your formats. The first time the puller scans a folder, it surfaces what it found and asks you to confirm which signals are real for that folder. From that point on, the folder is biased toward exactly those signals, and the puller behaves like every other connector: high-confidence proposals auto-accept on schedule, the rest queue for review. Calibration is one-time, per folder, and editable.
For organizations that already standardize on S3-compatible storage for security exports (most do, in some form), the puller turns that storage into a continuous KRI ingestion path with no extra plumbing. Drop a vendor SOC 2 into a bucket once a quarter, and the relevant control attestations land in the Risk Register the same day.
Security Posture
The Drop Zone is built to fit in a regulated environment, not around it.
- Local-only vendor. Artifacts never leave Draxis except for the bounded Sonnet inference call. No third-party processing, no SSRF surface, no "the data went where?" moment.
- 5 MB cap, enforced at three layers. Body parser, multipart upload, and webhook handler all reject oversized payloads with HTTP 413 before the LLM is ever called.
- Least-privilege S3 access. The puller supports both static access keys (with a documented minimal IAM policy: List + Get on the prefix, plus Delete or Put if you use post-process actions) and AssumeRole with an external ID, which is the recommended path. The external ID prevents the confused-deputy class of mistakes across tenants.
- Webhook tokens rotate on demand. Tokens are issued at save and rotate from the integration's detail page. Old tokens are revoked the moment a new one is issued.
- No silent drops. Failed extractions (timeouts, rate limits, malformed JSON from the model) record the failure reason on the artifact and surface in Pending extraction review for re-trigger. The Drop Zone never quietly loses an artifact.
- Truncation is explicit. Documents over the 200K-character working window are truncated from the end, and the artifact record carries an explicit
truncated: truestamp so reviewers know the extraction is not based on the whole document.
What the Drop Zone Is Not
The Drop Zone is deliberately scoped, and what it doesn't do is part of why the things it does do are trustworthy.
- Not a substitute for structured connectors. If a vendor has a Draxis connector (Okta, CrowdStrike, Tenable, Splunk, etc.), use it. Connectors run on schedule, cover more signals, and don't depend on whether someone remembered to upload a file. The Drop Zone is for the long tail.
- Not a free-text Q&A surface. The Drop Zone extracts typed KRI values against the catalog. To ask "what does this report mean for our risk?", use the AI vCISO panel, it consumes the extracted KRIs as part of its grounding context.
- Not a document store. Artifacts are persisted with their SHA-256 for audit and dedupe, but the Drop Zone is not a content-management system. Use it as the on-ramp for risk signal that lives in those documents, not as a filing cabinet.
- Not authorized to mutate analyst-owned state. Accepted extractions write KRI values. They do not change risk likelihood or impact, control effectiveness, or any other field an analyst owns. Those still flow through the AI Risk Score Proposals queue and explicit human review.
Why It Matters
Most cyber risk platforms are bounded by the connectors they ship with. The AI Drop Zone unbounds the Risk Register: any tool that can produce a file or a webhook payload, or write to an S3 bucket, can now feed it. The signal that used to die in someone's inbox now flows through the same model that prices loss, drafts the board narrative, and grounds the AI vCISO's answers.
For partners running multiple client tenants, the leverage is even higher. A vCISO who would otherwise spend an hour per client per quarter manually transcribing pentest findings now points the puller at a folder and walks away.
"The hardest part of running a real risk program isn't the connector you have, it's the report you don't have a connector for. We built the Drop Zone so that nothing with risk signal in it has to die in someone's inbox just because it didn't come with an API."| Draxis.ai
Availability
Both integrations are available today across all Draxis.ai tiers:
- SMB tier ($2,500/mo), AI Drop Zone and S3 puller included. One organization, with business units at $500/mo each.
- Partners tier (from $799/mo Practice), available across every client tenant, with per-tenant calibration profiles and the same volume tier economics on every billed tenant.
- Enterprise tier (custom), unlimited usage, custom integrations, and dedicated support.
Setup documentation is live in the support hub: AI Drop Zone and AI Drop Zone S3 puller.
Drop your first artifact
Paste a pentest report, upload a vendor SOC 2, or point the puller at an S3 bucket. See the Risk Register populate in seconds.
Get Early Access →About Draxis.ai
Draxis.ai is the AI-first cyber risk intelligence platform. It reads the security tools you already run, extracts typed Key Risk Indicators, and translates them into the financial exposure, operational risk, regulatory liability, and reputational impact your board, your insurer, and your regulators are asking about. Used by companies managing their own risk posture and by vCISO advisory firms scaling across multiple clients, Draxis.ai provides multi-tenant isolation, financial risk quantification, and full traceability from security tools to business impact.
Media contact: press@draxis.ai